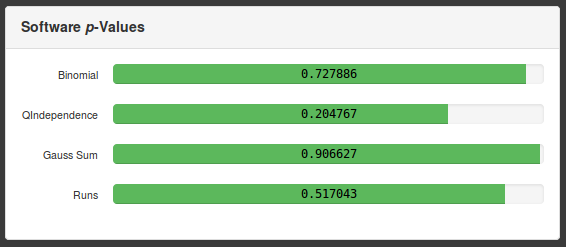
It’s been a busy Sunday, putting some embedded QA time towards our product’s inline entropy validation. Right now we have four statistical tests that constantly comb over each produced bit of randomness looking for suspicious patterns (i.e., patterns) from our generators. We chose each test not just to provide general warm fuzzies that our noise does in fact sound like noise, but because each targets its own type of data peculiarity - one test spots the characteristic repetition of weak generators like LCG, another roots out distributions of N-bit words that are too skew or not skew enough. All of them can be expressed as a single p-value, and are of course readily available to the user in pretty graphs like this:
Most modern cryptosystems depend on high-quality randomness, and this is truer of One Time Pad more than any other. The other guys might get away with seeding a software pseudorandom generator with a few environment-provided bytes, but we’re not generating hundreds of bits, we’re generating hundreds of billions. Total confidentiality demands it. And that’s what these tests are for - they provide some real-time assurances that our RNGs are doing what they ought to be: producing streams of independent, unguessable bits.
In a very real way, though, we’re the last people who ought to be trusted with providing these assurances. Should you rely on our self-validation? Of course not. So we built some mechanisms into our product to make independent verification easy. Here’s how to subject our box to an external randomness test suite (in this case, dieharder) in three easy steps:
-
Get dieharder
# sudo apt-get install dieharder -
Access the raw output of our generators. We provide access to hardware entropy on TCP port 780, and access to our environmental software generator on TCP port 781. Netcat works great. Grab a screenfull (where 1.9.8.4 is your red-side IP address)
# nc 1.9.8.4 780 | dd bs=1K count=1 | od -h -
If that works, start hammering. Just remember that the fine folks at Duke’s physics department have built a pretty comprehensive test suite, so grab a drink, a good book, and get a good night’s sleep. It should be done by the time you get home from work the next day.
# nc 1.9.8.4 780 | dieharder -g 200 -a
Here are the results of my run against the software system:
#=============================================================================#
# dieharder version 3.31.1 Copyright 2003 Robert G. Brown #
#=============================================================================#
rng_name |rands/second| Seed |
stdin_input_raw| 3.49e+05 |2479699573|
#=============================================================================#
test_name |ntup| tsamples |psamples| p-value |Assessment
#=============================================================================#
diehard_birthdays| 0| 100| 100|0.28295465| PASSED
diehard_operm5| 0| 1000000| 100|0.67623268| PASSED
diehard_rank_32x32| 0| 40000| 100|0.61628185| PASSED
diehard_rank_6x8| 0| 100000| 100|0.56191067| PASSED
diehard_bitstream| 0| 2097152| 100|0.99161044| PASSED
diehard_opso| 0| 2097152| 100|0.41625675| PASSED
diehard_oqso| 0| 2097152| 100|0.42833224| PASSED
diehard_dna| 0| 2097152| 100|0.67792705| PASSED
diehard_count_1s_str| 0| 256000| 100|0.41931322| PASSED
diehard_count_1s_byt| 0| 256000| 100|0.97999591| PASSED
diehard_parking_lot| 0| 12000| 100|0.14465251| PASSED
diehard_2dsphere| 2| 8000| 100|0.34302535| PASSED
diehard_3dsphere| 3| 4000| 100|0.06330664| PASSED
diehard_squeeze| 0| 100000| 100|0.13281998| PASSED
diehard_sums| 0| 100| 100|0.06235130| PASSED
diehard_runs| 0| 100000| 100|0.09425290| PASSED
diehard_runs| 0| 100000| 100|0.89388026| PASSED
diehard_craps| 0| 200000| 100|0.53686560| PASSED
diehard_craps| 0| 200000| 100|0.53155155| PASSED
marsaglia_tsang_gcd| 0| 10000000| 100|0.79553427| PASSED
marsaglia_tsang_gcd| 0| 10000000| 100|0.35502565| PASSED
sts_monobit| 1| 100000| 100|0.85756619| PASSED
sts_runs| 2| 100000| 100|0.50612971| PASSED
sts_serial| 1| 100000| 100|0.22148356| PASSED
sts_serial| 2| 100000| 100|0.06874334| PASSED
sts_serial| 3| 100000| 100|0.65308544| PASSED
sts_serial| 3| 100000| 100|0.00141914| WEAK
sts_serial| 4| 100000| 100|0.85418537| PASSED
sts_serial| 4| 100000| 100|0.67754880| PASSED
sts_serial| 5| 100000| 100|0.96926617| PASSED
sts_serial| 5| 100000| 100|0.76243532| PASSED
sts_serial| 6| 100000| 100|0.41278076| PASSED
sts_serial| 6| 100000| 100|0.62428928| PASSED
sts_serial| 7| 100000| 100|0.71365346| PASSED
sts_serial| 7| 100000| 100|0.51293711| PASSED
sts_serial| 8| 100000| 100|0.61264282| PASSED
sts_serial| 8| 100000| 100|0.39121480| PASSED
sts_serial| 9| 100000| 100|0.71509833| PASSED
sts_serial| 9| 100000| 100|0.98382945| PASSED
sts_serial| 10| 100000| 100|0.86978385| PASSED
sts_serial| 10| 100000| 100|0.98435912| PASSED
sts_serial| 11| 100000| 100|0.72733565| PASSED
sts_serial| 11| 100000| 100|0.95446412| PASSED
sts_serial| 12| 100000| 100|0.96433271| PASSED
sts_serial| 12| 100000| 100|0.88133415| PASSED
sts_serial| 13| 100000| 100|0.37709691| PASSED
sts_serial| 13| 100000| 100|0.13439558| PASSED
sts_serial| 14| 100000| 100|0.16230009| PASSED
sts_serial| 14| 100000| 100|0.22514747| PASSED
sts_serial| 15| 100000| 100|0.41219106| PASSED
sts_serial| 15| 100000| 100|0.64171102| PASSED
sts_serial| 16| 100000| 100|0.60200027| PASSED
sts_serial| 16| 100000| 100|0.14358061| PASSED
rgb_bitdist| 1| 100000| 100|0.72094831| PASSED
rgb_bitdist| 2| 100000| 100|0.93440127| PASSED
rgb_bitdist| 3| 100000| 100|0.70241749| PASSED
rgb_bitdist| 4| 100000| 100|0.97790030| PASSED
rgb_bitdist| 5| 100000| 100|0.03200904| PASSED
rgb_bitdist| 6| 100000| 100|0.81219879| PASSED
rgb_bitdist| 7| 100000| 100|0.58825413| PASSED
rgb_bitdist| 8| 100000| 100|0.31950545| PASSED
rgb_bitdist| 9| 100000| 100|0.34052576| PASSED
rgb_bitdist| 10| 100000| 100|0.17325100| PASSED
rgb_bitdist| 11| 100000| 100|0.75622620| PASSED
rgb_bitdist| 12| 100000| 100|0.40549436| PASSED
rgb_minimum_distance| 2| 10000| 1000|0.33076485| PASSED
rgb_minimum_distance| 3| 10000| 1000|0.97369574| PASSED
rgb_minimum_distance| 4| 10000| 1000|0.79788146| PASSED
rgb_minimum_distance| 5| 10000| 1000|0.66659128| PASSED
rgb_permutations| 2| 100000| 100|0.18541808| PASSED
rgb_permutations| 3| 100000| 100|0.07076327| PASSED
rgb_permutations| 4| 100000| 100|0.34442765| PASSED
rgb_permutations| 5| 100000| 100|0.53572428| PASSED
rgb_lagged_sum| 0| 1000000| 100|0.49341982| PASSED
rgb_lagged_sum| 1| 1000000| 100|0.91610503| PASSED
rgb_lagged_sum| 2| 1000000| 100|0.13450544| PASSED
rgb_lagged_sum| 3| 1000000| 100|0.61240506| PASSED
rgb_lagged_sum| 4| 1000000| 100|0.69897481| PASSED
rgb_lagged_sum| 5| 1000000| 100|0.69934657| PASSED
rgb_lagged_sum| 6| 1000000| 100|0.94988454| PASSED
rgb_lagged_sum| 7| 1000000| 100|0.99985319| WEAK
rgb_lagged_sum| 8| 1000000| 100|0.17079619| PASSED
rgb_lagged_sum| 9| 1000000| 100|0.83402873| PASSED
rgb_lagged_sum| 10| 1000000| 100|0.06451788| PASSED
rgb_lagged_sum| 11| 1000000| 100|0.25067624| PASSED
rgb_lagged_sum| 12| 1000000| 100|0.83888784| PASSED
rgb_lagged_sum| 13| 1000000| 100|0.10563819| PASSED
rgb_lagged_sum| 14| 1000000| 100|0.13235253| PASSED
rgb_lagged_sum| 15| 1000000| 100|0.36975820| PASSED
rgb_lagged_sum| 16| 1000000| 100|0.47723006| PASSED
rgb_lagged_sum| 17| 1000000| 100|0.96191331| PASSED
rgb_lagged_sum| 18| 1000000| 100|0.37532854| PASSED
rgb_lagged_sum| 19| 1000000| 100|0.93987088| PASSED
rgb_lagged_sum| 20| 1000000| 100|0.48103997| PASSED
rgb_lagged_sum| 21| 1000000| 100|0.48874024| PASSED
rgb_lagged_sum| 22| 1000000| 100|0.21224511| PASSED
rgb_lagged_sum| 23| 1000000| 100|0.06907080| PASSED
rgb_lagged_sum| 24| 1000000| 100|0.65006808| PASSED
rgb_lagged_sum| 25| 1000000| 100|0.54297610| PASSED
rgb_lagged_sum| 26| 1000000| 100|0.51703544| PASSED
rgb_lagged_sum| 27| 1000000| 100|0.65082437| PASSED
rgb_lagged_sum| 28| 1000000| 100|0.76185935| PASSED
rgb_lagged_sum| 29| 1000000| 100|0.85009808| PASSED
rgb_lagged_sum| 30| 1000000| 100|0.17664209| PASSED
rgb_lagged_sum| 31| 1000000| 100|0.76775656| PASSED
rgb_lagged_sum| 32| 1000000| 100|0.26895426| PASSED
rgb_kstest_test| 0| 10000| 1000|0.54332030| PASSED
dab_bytedistrib| 0| 51200000| 1|0.30751949| PASSED
dab_dct| 256| 50000| 1|0.12868842| PASSED
dab_filltree| 32| 15000000| 1|0.10016558| PASSED
dab_filltree| 32| 15000000| 1|0.06843607| PASSED
dab_filltree2| 0| 5000000| 1|0.33366611| PASSED
dab_filltree2| 1| 5000000| 1|0.64325956| PASSED
dab_monobit2| 12| 65000000| 1|0.73949048| PASSEDI’m proud to work on a team that doesn’t hand-wave. I can’t tell you how many security products I’ve used that make no mention - even in the fine print - of how they derive their randomness. None of us here at Prolaag would ever do that. We’ll put our raw data out there, front and center, for anyone who wants to double-check us.
